
Close

We enable business and digital transformation decisions through the delivery of cutting-edge ICT solutions and products...
The Internet is wonderfully useful. The autodidact no longer needs a library. The film aficionado can live without a cinema. But life is easier for the extortionist as well, who can rob hundreds of thousands of people at once while still in pyjamas. Such power was on ample display this weekend, when a large cyber-attack afflicted an estimated 200,000 computers in 150 countries.
The cyber-attack, dubbed “WannaCry”, was built to go global. It helpfully offers victims translations of its demand for money in 28 different languages, and does not discriminate much in its targets. Chinese universities, Russia’s interior ministry and Britain’s National Health Service (NHS) all saw their computer systems taken hostage in the attack. WannaCry is only the most recent example of “ransomware”, malicious programs that block access to files unless the victim pays off the hackers (usually in Bitcoin, an untraceable digital currency).
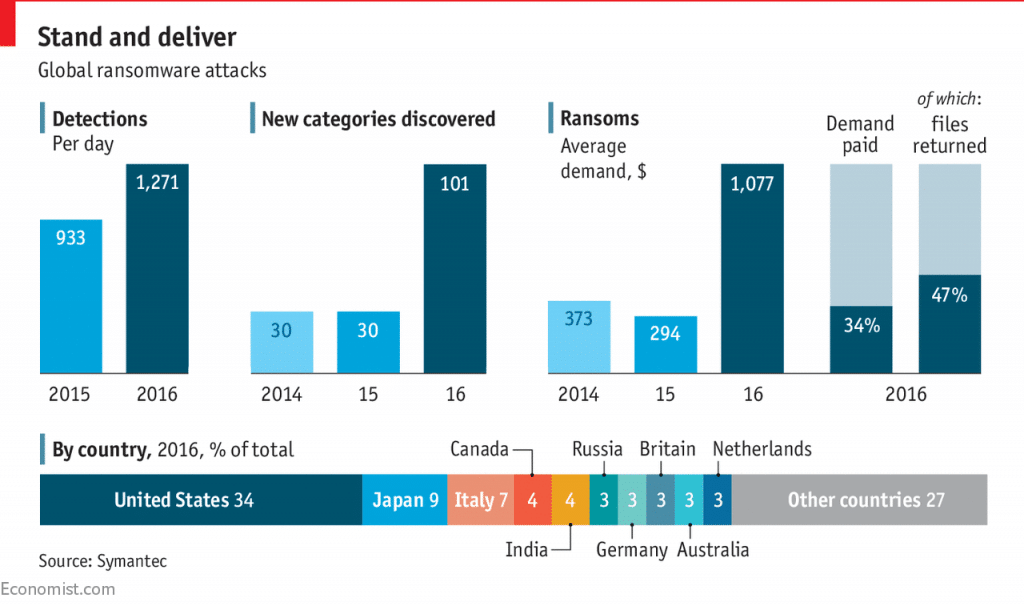
Since 2014 the varieties of ransomware have more than tripled, according to the Internet Security Threat Report by Symantec, a computer-security vendor—a sign that internet bandits are catching on to the lucrative rewards it offers. The FBI reckons that CryptoWall, a particularly nasty strain of ransomware, netted at least $18m for cyber-crooks in 2015. Hackers are also getting greedier: the average haul from a ransomware attack has gone up from $373 per victim in 2014 to $1,077 in 2016.
WannaCry demands a comparatively low payment of $300 worth of Bitcoin—though the price doubles if payment does not arrive within three days. Four Bitcoin “wallets” associated with the attackers have, at the last check, received 227 payments, worth a total of 35.53 Bitcoin (about $63,000).
By May 15th, the cyber-attack was spreading more slowly and the blame game had already begun. Its victims were all Windows users who had not updated their software—a process that is necessary but also cumbersome and costly for large organisations. Meanwhile, Microsoft has pointed the finger at American spooks: the National Security Agency originally discovered the vulnerabilities in Windows on which WannaCry relies, but did not notify the company until after it had been hacked and the exploit in question stolen and posted online. The spectacle of the NHS being brought to its knees by malware will surely focus the public’s attention on the vulnerability of critical infrastructure to covert, offensive cyber-attacks that Western governments would rather keep hidden.
By the Economist Data Team